HTB: Investigation
Por um escritor misterioso
Last updated 05 agosto 2024

Investigation starts with a website that accepts user uploaded images and runs Exiftool on them. This version has a command injection. I’ll dig into that vulnerability, and then exploit it to get a foothold. Then I find a set of Windows event logs, and analyze them to extract a password. Finally, I find a piece of malware that runs as root and understand it to get execution.
Hacking Around: Previse - HTB writeup - SecSI

Hack The Box - Investigation - WriteUP

PDF) Statistical Investigation of the Disturbances Affecting the Power Distribution Networks (HTB/HTA) of a Few Source Substations in South-Benin

Part 3: How the HTB research was done and what's coming up in the main chapters. – Your name is like honey

Hack The Box: Mango - L4r1k

After coming out, 'I had PTSD symptoms' says lay leader in church-plant

Hack The Box
Your 2023 cybersecurity resolutions - Hack The Box EU
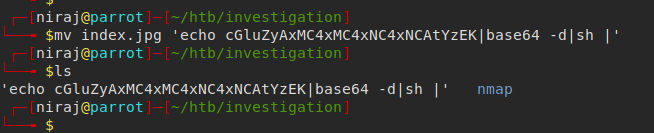
HTB — Investigation. A detailed walkthrough for solving…, by Niraj Kharel
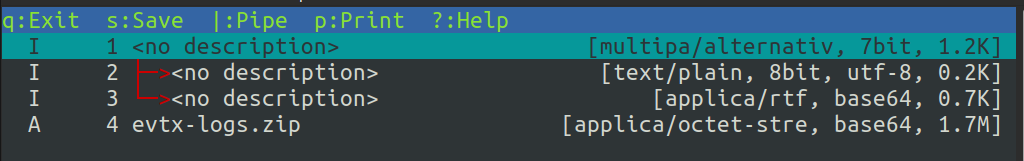
HTB: Investigation
Recomendado para você
-
Diep.io Mods, Tanks, Features, Guide05 agosto 2024
-
 Digdig.io Crazy Gameplay - JEHRO The Best of The game.!05 agosto 2024
Digdig.io Crazy Gameplay - JEHRO The Best of The game.!05 agosto 2024 -
 Dig The Dunes,dig the dunes quotes,04 Poster for Sale by john aql05 agosto 2024
Dig The Dunes,dig the dunes quotes,04 Poster for Sale by john aql05 agosto 2024 -
 Playable 2600 Dig Dug-arcade gfx hack! - Atari 2600 Hacks05 agosto 2024
Playable 2600 Dig Dug-arcade gfx hack! - Atari 2600 Hacks05 agosto 2024 -
 Help Tap Dig my museum - Requests - GameGuardian05 agosto 2024
Help Tap Dig my museum - Requests - GameGuardian05 agosto 2024 -
 Anthony J. D'Angelo Quote: “When solving problems, dig at the05 agosto 2024
Anthony J. D'Angelo Quote: “When solving problems, dig at the05 agosto 2024 -
 hacks to dig hole on red dirt|TikTok Search05 agosto 2024
hacks to dig hole on red dirt|TikTok Search05 agosto 2024 -
 Unboxing and Setup - Shark Jack05 agosto 2024
Unboxing and Setup - Shark Jack05 agosto 2024 -
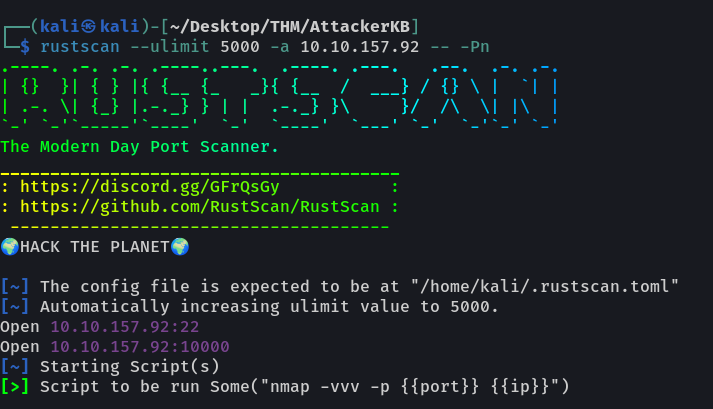 Try Hack Me: AttackerKB. Today we are going to look at…, by Ryan Yager05 agosto 2024
Try Hack Me: AttackerKB. Today we are going to look at…, by Ryan Yager05 agosto 2024 -
![Guide] Quick Tips on How To Keep Your Loop Safe (Don't be an idiot. Its heart breaking to read stories of how peoples hard earned money is stolen from them.) : r/loopringorg](https://preview.redd.it/bd8q7iz0ys681.png?auto=webp&s=84ef0fdccee111b8640a985cb3b77e1afcff25be) Guide] Quick Tips on How To Keep Your Loop Safe (Don't be an idiot. Its heart breaking to read stories of how peoples hard earned money is stolen from them.) : r/loopringorg05 agosto 2024
Guide] Quick Tips on How To Keep Your Loop Safe (Don't be an idiot. Its heart breaking to read stories of how peoples hard earned money is stolen from them.) : r/loopringorg05 agosto 2024
você pode gostar
-
![AOPG] KING'S FRUIT ATTACKS SHOWCASE SNEAK! A One Piece Game](https://i.ytimg.com/vi/aLVlxQs-AcE/maxresdefault.jpg) AOPG] KING'S FRUIT ATTACKS SHOWCASE SNEAK! A One Piece Game05 agosto 2024
AOPG] KING'S FRUIT ATTACKS SHOWCASE SNEAK! A One Piece Game05 agosto 2024 -
 Portugal vs. Switzerland final score, result: Ronaldo replacement Ramos nets hat-trick in World Cup Round of 1605 agosto 2024
Portugal vs. Switzerland final score, result: Ronaldo replacement Ramos nets hat-trick in World Cup Round of 1605 agosto 2024 -
Oculos Juliet Oakley, Óculos Feminino Oakley Nunca Usado 5405113005 agosto 2024
-
![Problem!] Roblox banned me for no reason (SFM) by PhillyWasPM on DeviantArt](https://images-wixmp-ed30a86b8c4ca887773594c2.wixmp.com/f/2aab0b8c-e79c-4b29-9b1a-159e32b14dc0/dfr45hn-aec5375b-c1bf-43f5-92bc-7d7643f5dd32.png?token=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJzdWIiOiJ1cm46YXBwOjdlMGQxODg5ODIyNjQzNzNhNWYwZDQxNWVhMGQyNmUwIiwiaXNzIjoidXJuOmFwcDo3ZTBkMTg4OTgyMjY0MzczYTVmMGQ0MTVlYTBkMjZlMCIsIm9iaiI6W1t7InBhdGgiOiJcL2ZcLzJhYWIwYjhjLWU3OWMtNGIyOS05YjFhLTE1OWUzMmIxNGRjMFwvZGZyNDVobi1hZWM1Mzc1Yi1jMWJmLTQzZjUtOTJiYy03ZDc2NDNmNWRkMzIucG5nIn1dXSwiYXVkIjpbInVybjpzZXJ2aWNlOmZpbGUuZG93bmxvYWQiXX0.nu_rB2iWm58pLPA1J_UOgJFHoy3OlQCQQispx7oaN5U) Problem!] Roblox banned me for no reason (SFM) by PhillyWasPM on DeviantArt05 agosto 2024
Problem!] Roblox banned me for no reason (SFM) by PhillyWasPM on DeviantArt05 agosto 2024 -
 Planet Clicker - Jogar de graça05 agosto 2024
Planet Clicker - Jogar de graça05 agosto 2024 -
 Pin by mieseyo on Aesthetic- Background- Wallpaper in 202305 agosto 2024
Pin by mieseyo on Aesthetic- Background- Wallpaper in 202305 agosto 2024 -
.jpg) Assassin's Creed Valhalla Arabic And English PS505 agosto 2024
Assassin's Creed Valhalla Arabic And English PS505 agosto 2024 -
 Vasco da Gama – Liga Nacional de Basquete05 agosto 2024
Vasco da Gama – Liga Nacional de Basquete05 agosto 2024 -
Steam Workshop::SCP 300805 agosto 2024
-
 Ferrari Vision Gran Turismo: gamers' delight heading to GT705 agosto 2024
Ferrari Vision Gran Turismo: gamers' delight heading to GT705 agosto 2024