Malware analysis Malicious activity
Por um escritor misterioso
Last updated 14 julho 2024

Malware analysis index.html Malicious activity

Robust Malware Detection Models: Learning From Adversarial Attacks and Defenses - Forensic Focus

AV-TEST Confirms Skyhigh Security Service Edge Delivers Superior Threat Protection in All Test Categories

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac

TryHackMe Hacktivities

Malware Analysis: Steps & Examples - CrowdStrike
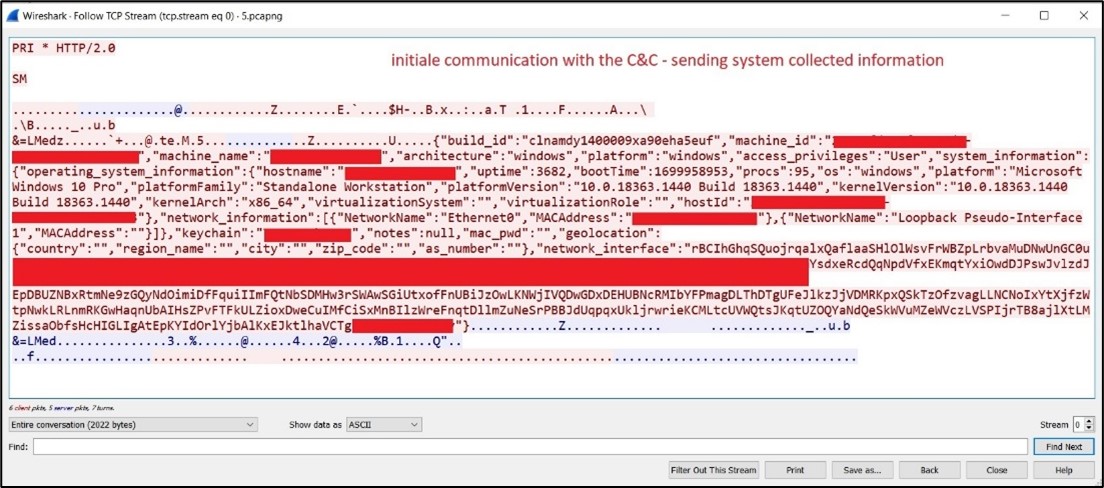
Behind the Scenes: JaskaGO's Coordinated Strike on macOS and Windows

Malware analysis cd53fba6ddd4ae4ef7a5747c6003236c85791477854cc1b7ce00e0f8ee7677d9 Malicious activity

Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious activity

Malware analysis Program_Install_and_Uninstall Malicious activity

Endpoint Detection and Response, Free - What is EDR Security?
Recomendado para você
-
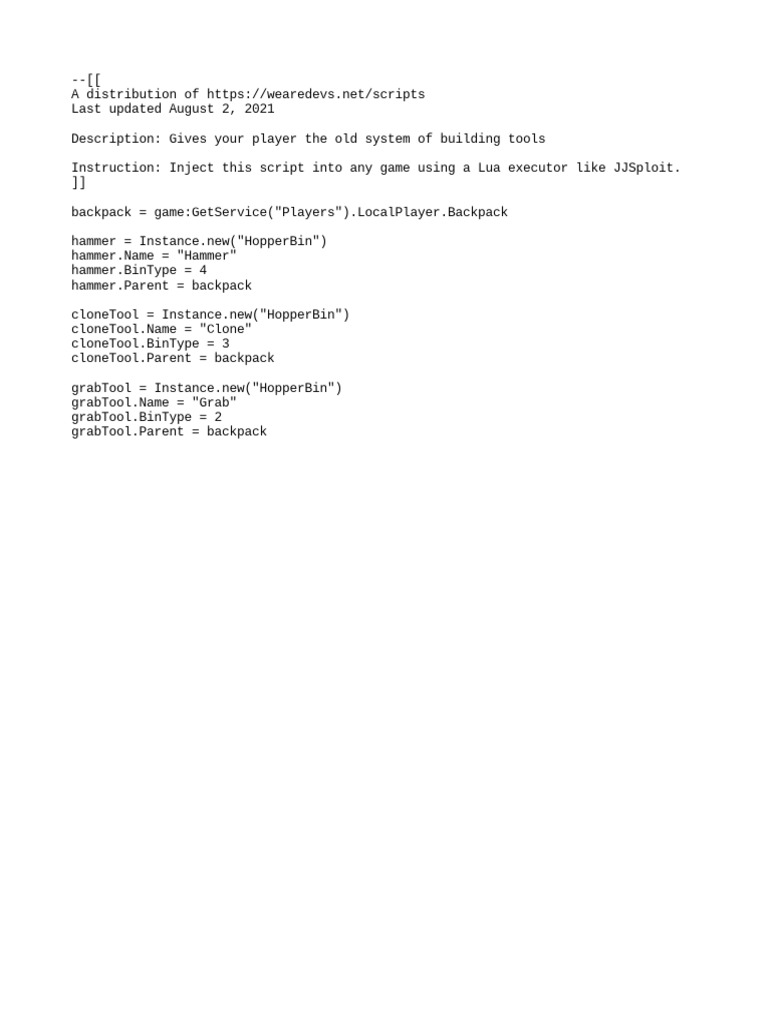
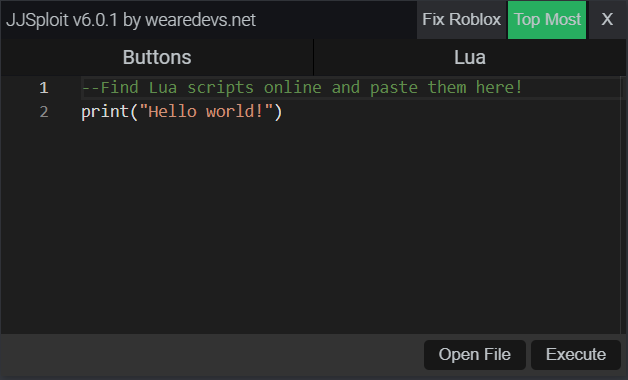 JJSploit Information - WeAreDevs14 julho 2024
JJSploit Information - WeAreDevs14 julho 2024 -
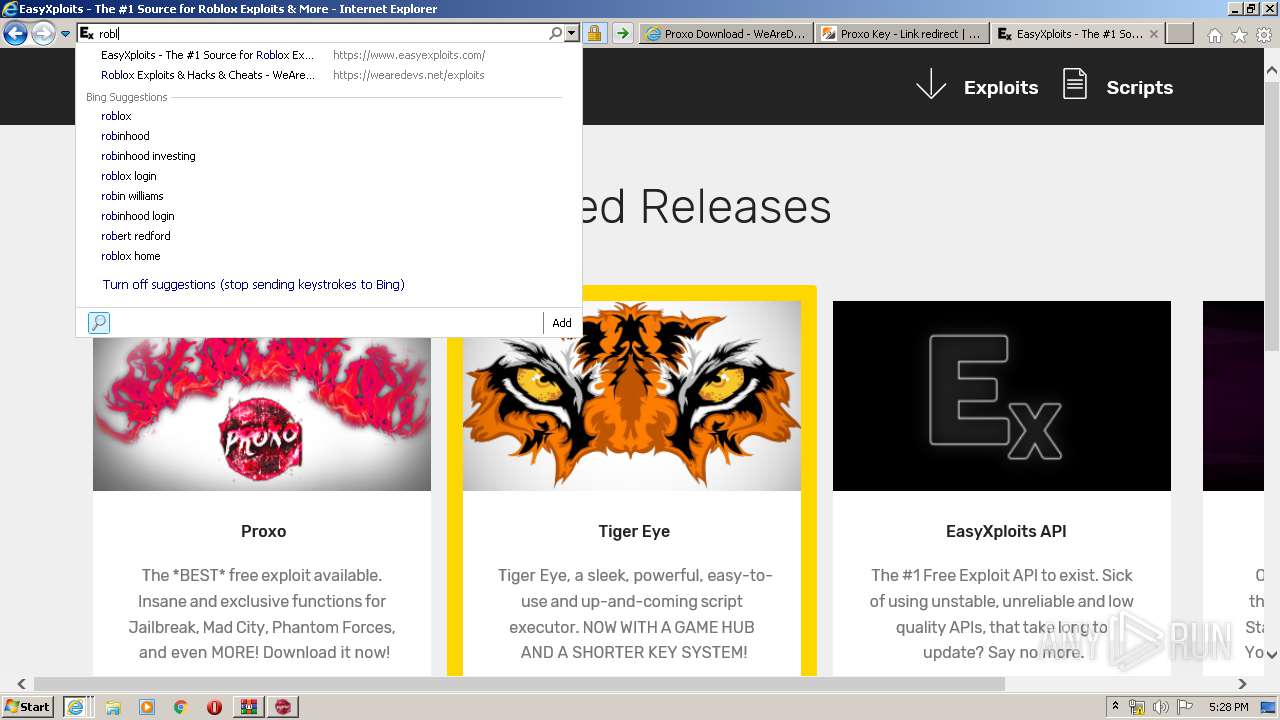
 Proxo Download Page, WeAreDevs14 julho 2024
Proxo Download Page, WeAreDevs14 julho 2024 -
 How to use lua scripts with JJ sploit (By wearedevs)14 julho 2024
How to use lua scripts with JJ sploit (By wearedevs)14 julho 2024 -
BTools14 julho 2024
-
 How to dowload and use Krnl and scripts!14 julho 2024
How to dowload and use Krnl and scripts!14 julho 2024 -
 IT Pro Tuesday #19014 julho 2024
IT Pro Tuesday #19014 julho 2024 -
roblox #fyo #hack #script #jjsploit #wearedevs Like and Comment “tuto14 julho 2024
-
roblox-executor · GitHub Topics · GitHub14 julho 2024
-
 Malware analysis Malicious14 julho 2024
Malware analysis Malicious14 julho 2024 -
 Exploiter kicking everyone from the server, how to find who? - Scripting Support - Developer Forum14 julho 2024
Exploiter kicking everyone from the server, how to find who? - Scripting Support - Developer Forum14 julho 2024
você pode gostar
-
The End Games - Fastest hands this side of the Mississippi.14 julho 2024
-
Tradução de One Piece14 julho 2024
-
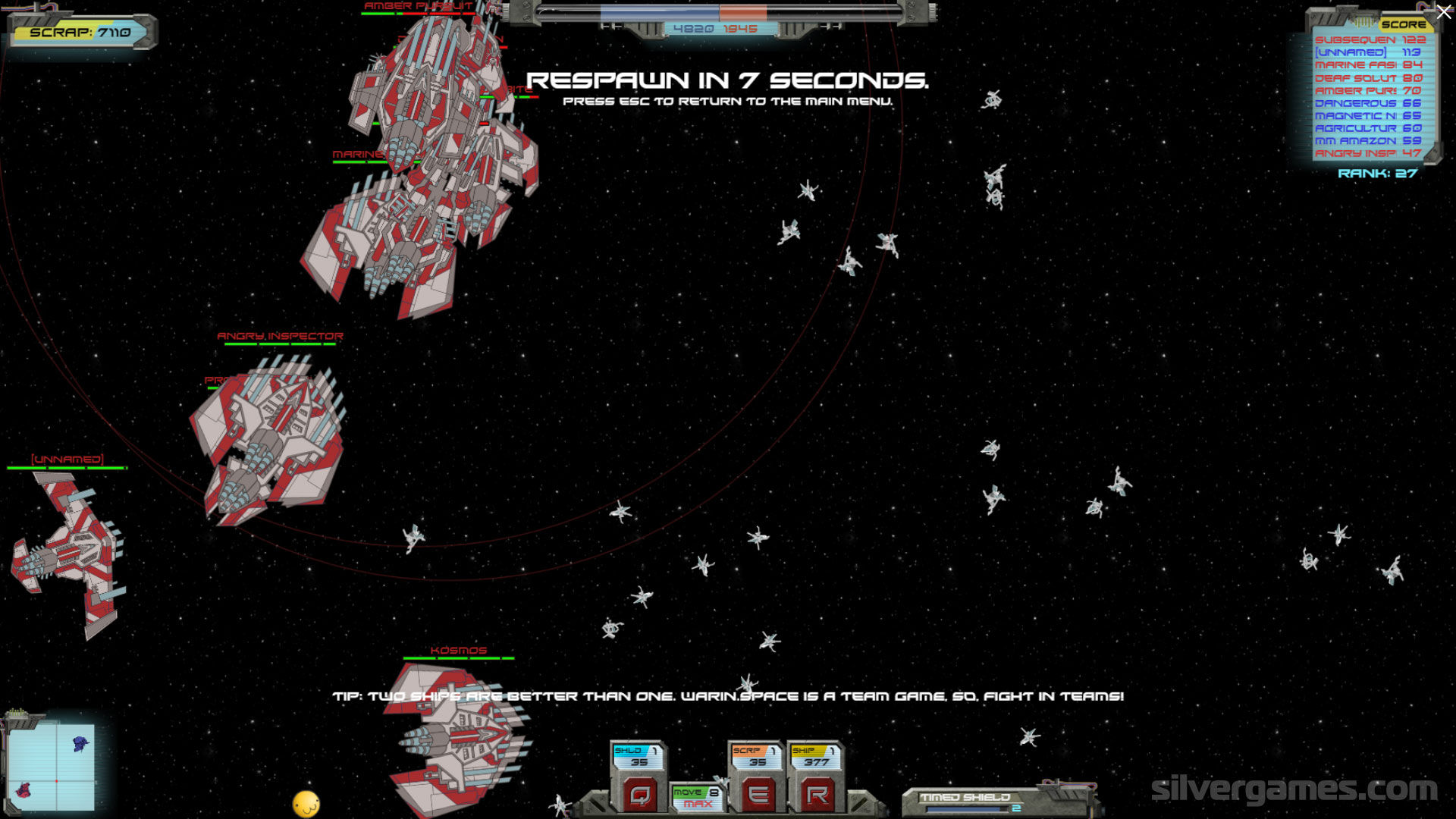 War In Space - Play Online on SilverGames 🕹️14 julho 2024
War In Space - Play Online on SilverGames 🕹️14 julho 2024 -
Talking Tom Time Rush Ver. 1.0.44.16992 MOD Menu APK14 julho 2024
-
/origin-imgresizer.eurosport.com/2021/07/07/3169271-64940868-2560-1440.jpg) Wimbledon 2021 tennis - Inspired Hubert Hurkacz downs Roger Federer in huge shock at Wimbledon - Eurosport14 julho 2024
Wimbledon 2021 tennis - Inspired Hubert Hurkacz downs Roger Federer in huge shock at Wimbledon - Eurosport14 julho 2024 -
 Sapnap Dream Team+BreezeWiki14 julho 2024
Sapnap Dream Team+BreezeWiki14 julho 2024 -
 Essential Madeira Islands N.º 87 by Open Media Atlantic - Issuu14 julho 2024
Essential Madeira Islands N.º 87 by Open Media Atlantic - Issuu14 julho 2024 -
 Concours pour la comédie, scène nationale de Clermont-Ferrand - D14 julho 2024
Concours pour la comédie, scène nationale de Clermont-Ferrand - D14 julho 2024 -
![AmiAmi [Character & Hobby Shop] KAITAI FANTASY Sanrio Characters Fancy Purple 4Pack BOX(Released)](https://img.amiami.com/images/product/main/224/GOODS-04284034.jpg) AmiAmi [Character & Hobby Shop] KAITAI FANTASY Sanrio Characters Fancy Purple 4Pack BOX(Released)14 julho 2024
AmiAmi [Character & Hobby Shop] KAITAI FANTASY Sanrio Characters Fancy Purple 4Pack BOX(Released)14 julho 2024 -
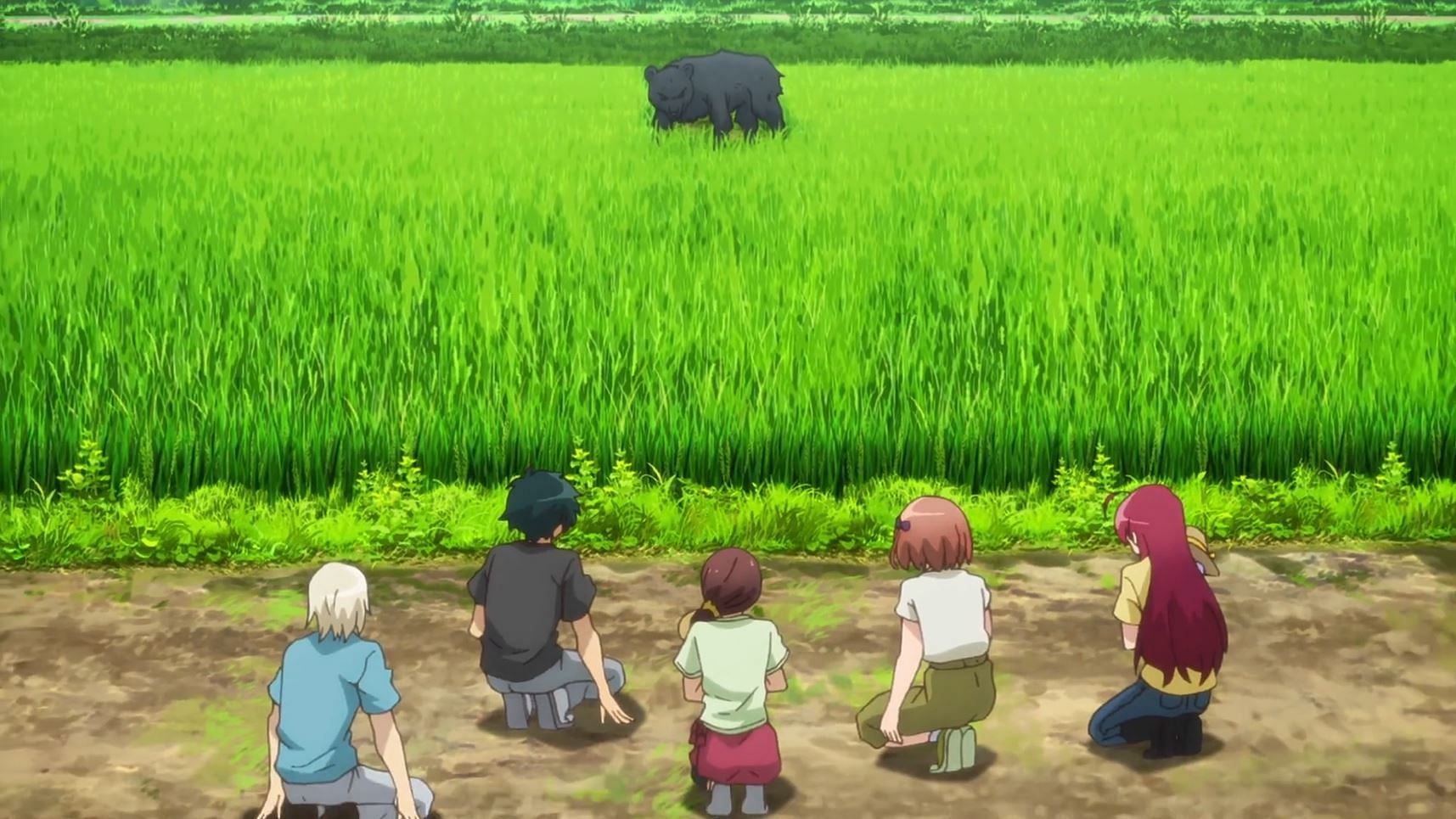 The Devil is a Part-Timer!! Season 2 Episode 8: Bear sneaks in, peril at Sasaki farms14 julho 2024
The Devil is a Part-Timer!! Season 2 Episode 8: Bear sneaks in, peril at Sasaki farms14 julho 2024