Pawn Storm Abuses OAuth In Social Engineering Attacks
Por um escritor misterioso
Last updated 04 julho 2024
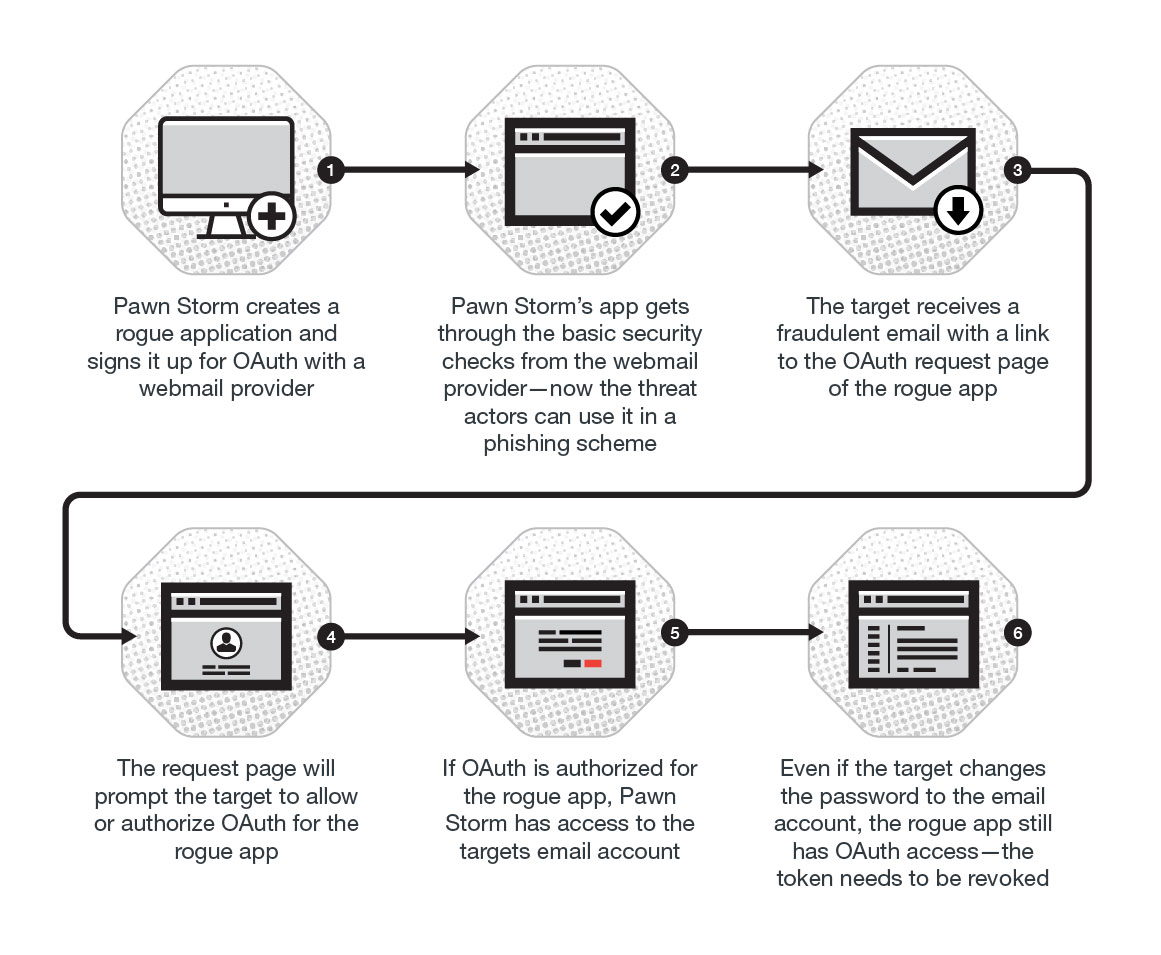
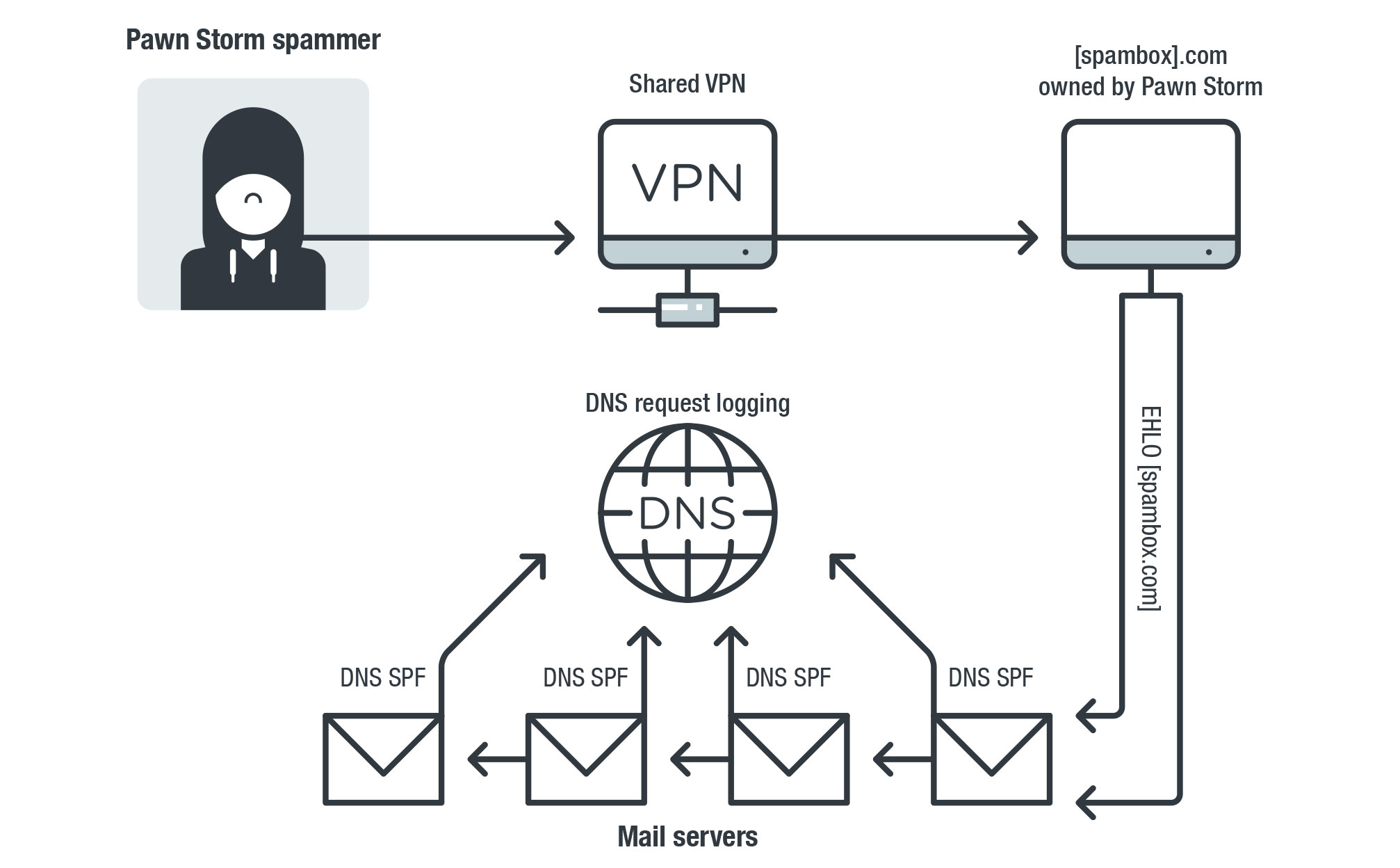
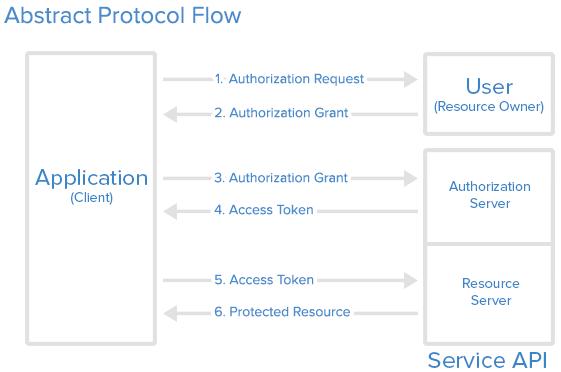
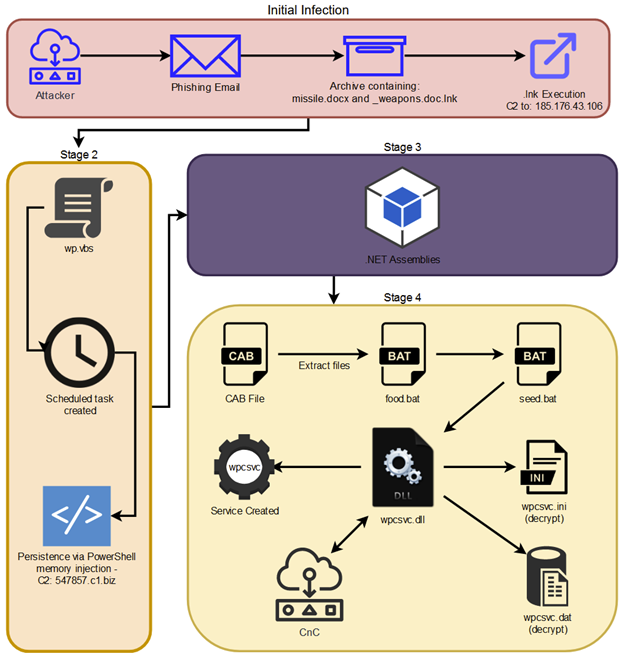
This blog post discusses how Pawn Storm abused Open Authentication (OAuth) in advanced social engineering schemes. High profile users of free webmail were targeted by campaigns between 2015 and 2016.
DEF CON 29 - TIB AV-Portal
Must Read - Security Affairs

Salt Labs Oh-Auth - Abusing OAuth to take over millions of accounts
Probing Pawn Storm: Cyberespionage Campaign Through Scanning, Credential Phishing and More - Security News

Ontological Model of a Social Engineering Attack [in accordance with 10].
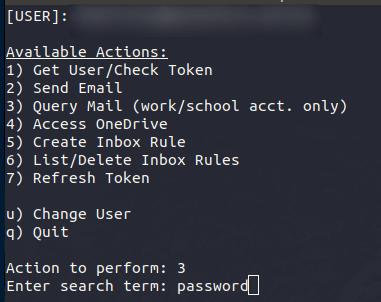
Oauth Token Stealing - Red Team Blog
Oauth Token Stealing - Red Team Blog
APT28 Archives - Security Affairs
GitHub - netskopeoss/phish_oauth: POC code to explore phishing attacks using OAuth 2.0 authorization flows, such as the device authorization grant.
Pawn Storm's Lack of Sophistication as a Strategy
What are Social Engineering Attacks? Types of Attacks in 2023
Recomendado para você
-
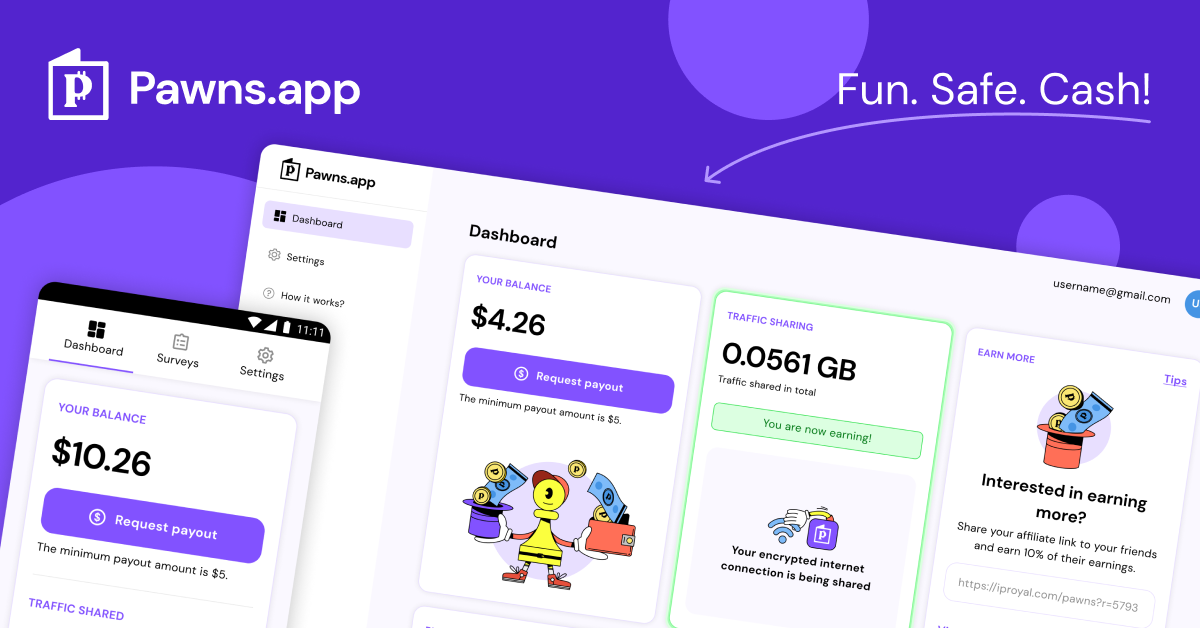 IPRoyal Pawns Just Became - Pawns04 julho 2024
IPRoyal Pawns Just Became - Pawns04 julho 2024 -
 Download our APP! La Familia Pawn and Jewelry04 julho 2024
Download our APP! La Familia Pawn and Jewelry04 julho 2024 -
 Pawns.app: Share Internet to Earn Demo video by MobileAppDaily04 julho 2024
Pawns.app: Share Internet to Earn Demo video by MobileAppDaily04 julho 2024 -
 Residential Proxy IP Networks: What Everyone in Ad Tech Needs to Know - AdMonsters04 julho 2024
Residential Proxy IP Networks: What Everyone in Ad Tech Needs to Know - AdMonsters04 julho 2024 -
Pawns.app Reviews, Read Customer Service Reviews of pawns.app04 julho 2024
-
Pawns.app on LinkedIn: 10 Ways to Boost Your Summer Savings and Not Get Burned - Pawns04 julho 2024
-
 How humanitarian aid in Gaza is being used as an instrument of war - Los Angeles Times04 julho 2024
How humanitarian aid in Gaza is being used as an instrument of war - Los Angeles Times04 julho 2024 -
 Pawns App Review - New, Ultimate and Comprehensive04 julho 2024
Pawns App Review - New, Ultimate and Comprehensive04 julho 2024 -
COMING TO THE SHOW? KNOW BEFORE YOU GO! Doors- 6 PM Pawn Shop Pearls on the Honky Tonk Stage - 8 PM @eliyoungband on the Main Stage -…04 julho 2024
-
 O que é Pawns.App e Como Funciona? ( Review 2023 )04 julho 2024
O que é Pawns.App e Como Funciona? ( Review 2023 )04 julho 2024
você pode gostar
-
 Hyakuren No Haou To Seiyaku No Valkyria04 julho 2024
Hyakuren No Haou To Seiyaku No Valkyria04 julho 2024 -
 Prime Video: Scorching Ping Pong Girls: Season 104 julho 2024
Prime Video: Scorching Ping Pong Girls: Season 104 julho 2024 -
 QR codes can be manipulated to steal from you, FBI warns04 julho 2024
QR codes can be manipulated to steal from you, FBI warns04 julho 2024 -
 Dante's Inferno trailer highlights story and gameplay - Neoseeker04 julho 2024
Dante's Inferno trailer highlights story and gameplay - Neoseeker04 julho 2024 -
 God of War (TV Series) - IMDb04 julho 2024
God of War (TV Series) - IMDb04 julho 2024 -
 Mandalorian Hasbro Star Wars Electronic The Darksaber Light & Sound Sword Toy04 julho 2024
Mandalorian Hasbro Star Wars Electronic The Darksaber Light & Sound Sword Toy04 julho 2024 -
 hard would you rather questions to answer|TikTok Search04 julho 2024
hard would you rather questions to answer|TikTok Search04 julho 2024 -
 Snakes & Ladders04 julho 2024
Snakes & Ladders04 julho 2024 -
 Grêmio empata com Cruzeiro no primeiro jogo das oitavas de final da Copa do Brasil04 julho 2024
Grêmio empata com Cruzeiro no primeiro jogo das oitavas de final da Copa do Brasil04 julho 2024 -
 E-JET GAME Basketball Arcade Games (Online Battle and Challenge, Shoot Hoops)- Electronic Arcade Basketball Games, Dual Shot- Purple in the Electronic Basketball Games department at04 julho 2024
E-JET GAME Basketball Arcade Games (Online Battle and Challenge, Shoot Hoops)- Electronic Arcade Basketball Games, Dual Shot- Purple in the Electronic Basketball Games department at04 julho 2024