Validating User Flows to Protect Software Defined Network Environments
Por um escritor misterioso
Last updated 06 julho 2024

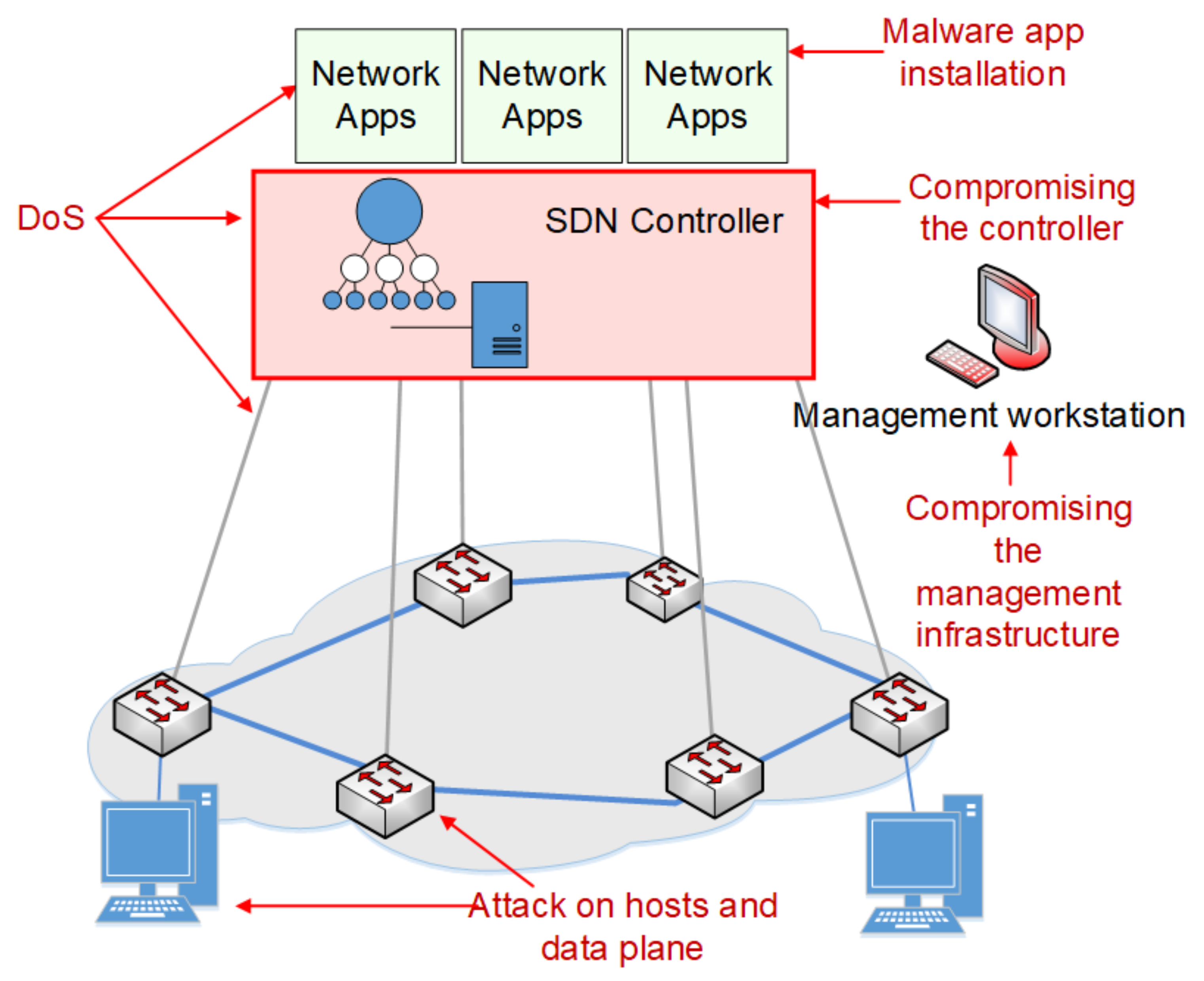
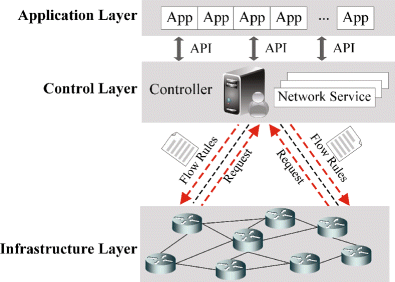
Software Defined Network is a promising network paradigm which has led to several security threats in SDN applications that involve user flows, switches, and controllers in the network. Threats as spoofing, tampering, information disclosure, Denial of Service, flow table overloading, and so on have been addressed by many researchers. In this paper, we present novel SDN design to solve three security threats: flow table overloading is solved by constructing a star topology-based architecture, unsupervised hashing method mitigates link spoofing attack, and fuzzy classifier combined with L1-ELM running on a neural network for isolating anomaly packets from normal packets. For effective flow migration Discrete-Time Finite-State Markov Chain model is applied. Extensive simulations using OMNeT++ demonstrate the performance of our proposed approach, which is better at preserving holding time than are other state-of-the-art works from the literature.
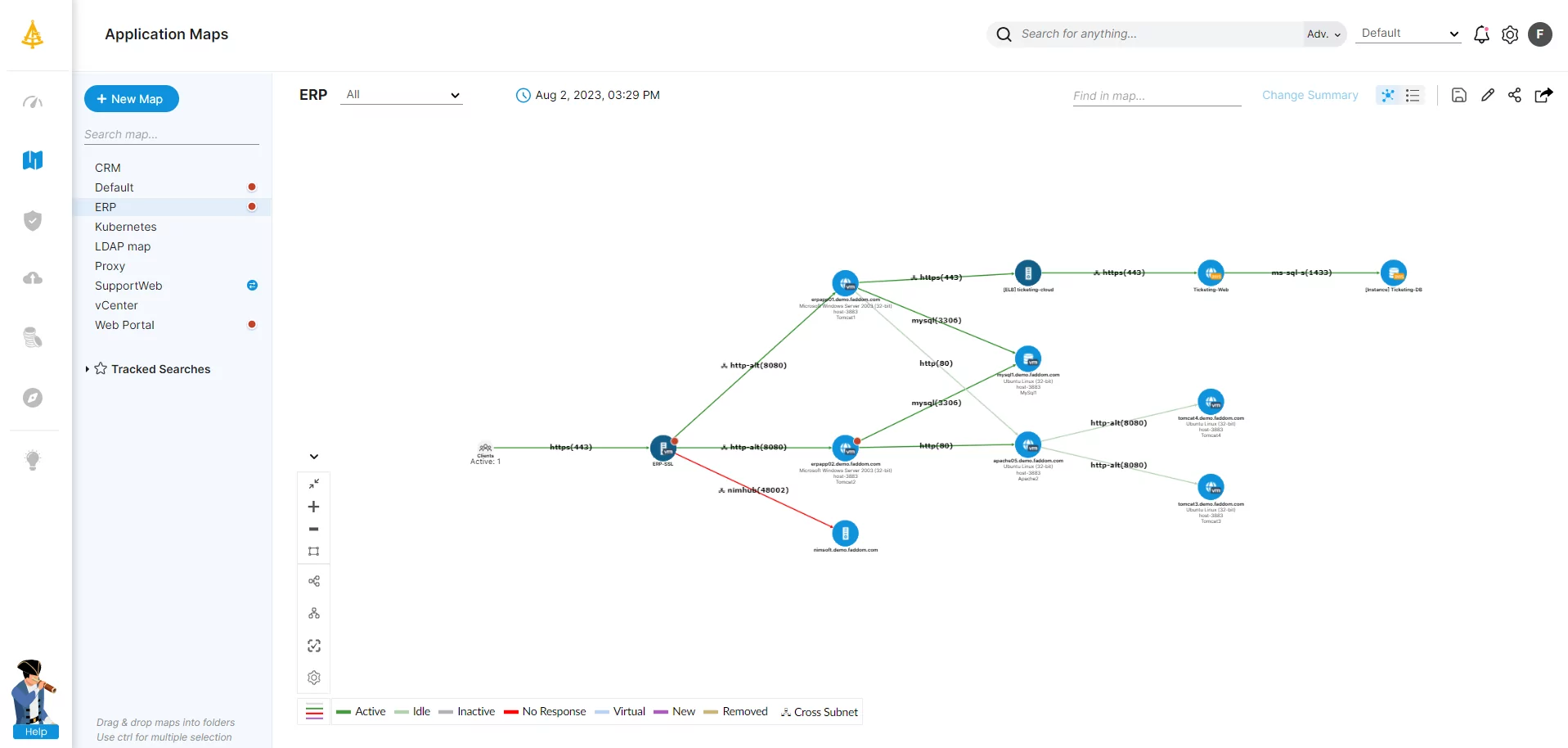
Application Dependency Mapping: The Complete Guide
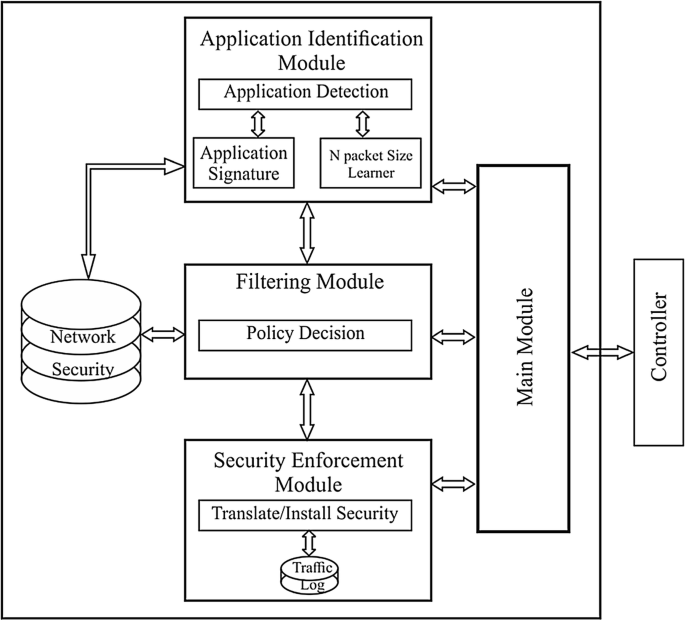
Application-Aware Firewall Mechanism for Software Defined Networks
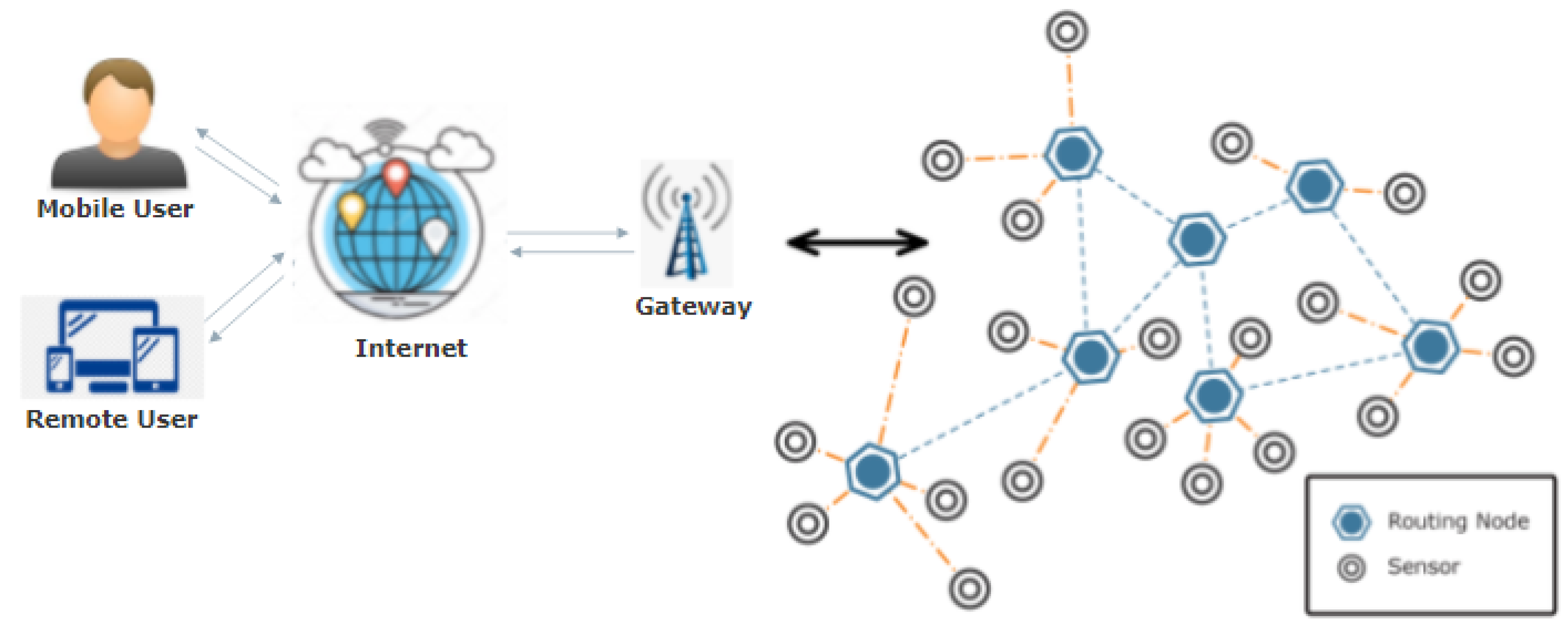
Sensors, Free Full-Text

Validating User Flows to Protect Software Defined Network Environments

Validating User Flows to Protect Software Defined Network Environments
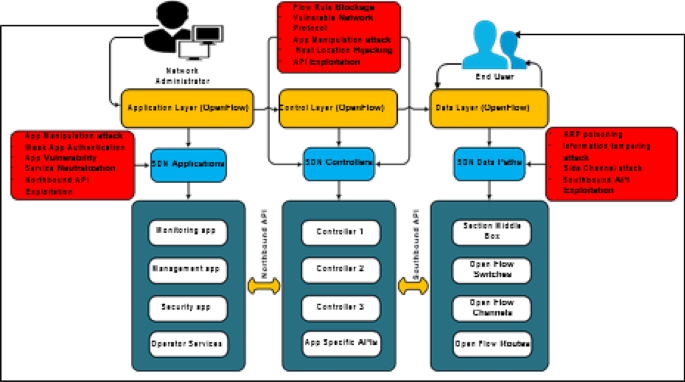
Security & Privacy in Software Defined Networks, Issues
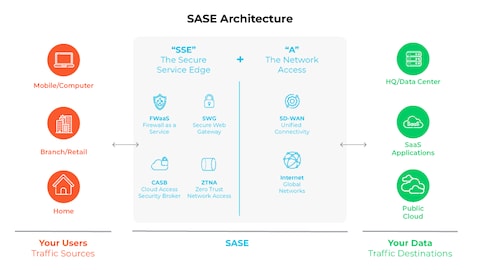
What Is SASE? - Palo Alto Networks
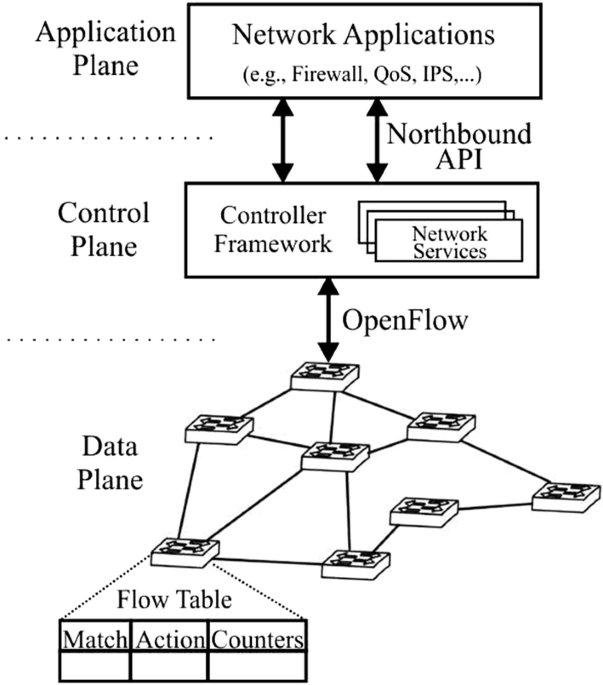
Application-Aware Firewall Mechanism for Software Defined Networks

Software-defined wireless network (SDWN): A new paradigm for next

Managing multi-tenant APIs using API Gateway
Sensors, Free Full-Text
PERM-GUARD: Authenticating the Validity of Flow Rules in Software

Recommendations for networking and connectivity - Microsoft Azure
How Netflix uses eBPF flow logs at scale for network insight
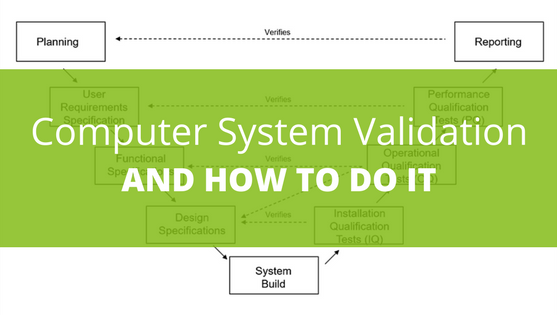
What is Computer System Validation and How Do You Do It?
Recomendado para você
-
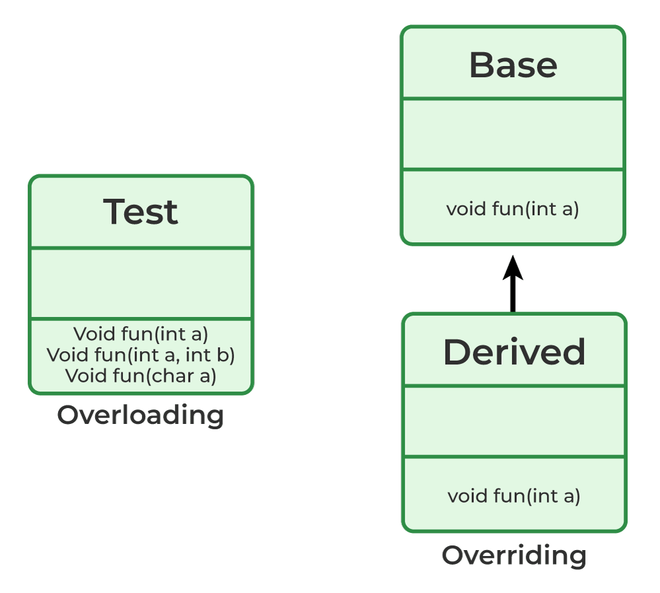 Method Overloading in Java - GeeksforGeeks06 julho 2024
Method Overloading in Java - GeeksforGeeks06 julho 2024 -
 Method overriding - Wikipedia06 julho 2024
Method overriding - Wikipedia06 julho 2024 -
Australian Open: Seagull Poo Delayed Muguruza Vs. Konta Match06 julho 2024
-
 Side Effects of Holding in Poop: What You Should Know06 julho 2024
Side Effects of Holding in Poop: What You Should Know06 julho 2024 -
 Addressing withholding behaviours in infants and children with constipation06 julho 2024
Addressing withholding behaviours in infants and children with constipation06 julho 2024 -
 Soiling - ERIC06 julho 2024
Soiling - ERIC06 julho 2024 -
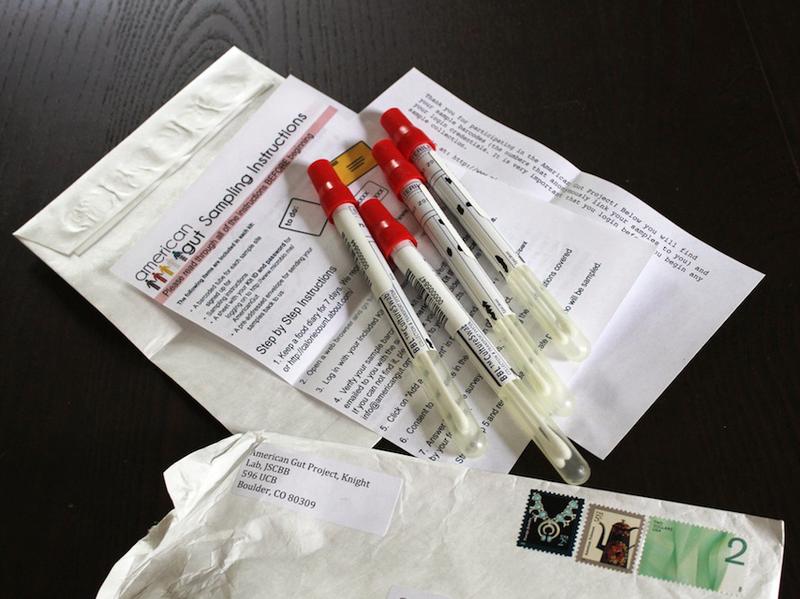
To Get To The Bottom Of Your Microbiome, Start With A Swab Of Poo, NPR Article06 julho 2024
-
 Cooling cabinet Williams. - PS Auction - We value the future - Largest in net auctions06 julho 2024
Cooling cabinet Williams. - PS Auction - We value the future - Largest in net auctions06 julho 2024 -
 Graphical User Interface of POO SG.06 julho 2024
Graphical User Interface of POO SG.06 julho 2024 -
 A Probiotic Cocktail Made From Baby Poo Could Help Improve Gut Health06 julho 2024
A Probiotic Cocktail Made From Baby Poo Could Help Improve Gut Health06 julho 2024
você pode gostar
-
 Twitch, League of Legends Wiki, FANDOM powered by Wikia06 julho 2024
Twitch, League of Legends Wiki, FANDOM powered by Wikia06 julho 2024 -
 Camiseta masculina premium branca caveira preta - JOHN VERDAZZI06 julho 2024
Camiseta masculina premium branca caveira preta - JOHN VERDAZZI06 julho 2024 -
 Gearhumans 3D Devil Fruits Ope Ope No Mi Custom Ornament06 julho 2024
Gearhumans 3D Devil Fruits Ope Ope No Mi Custom Ornament06 julho 2024 -
![DJ's Pokémon Type Meme by Chinca -- Fur Affinity [dot] net](https://t.furaffinity.net/2907593@600-1255392277.jpg) DJ's Pokémon Type Meme by Chinca -- Fur Affinity [dot] net06 julho 2024
DJ's Pokémon Type Meme by Chinca -- Fur Affinity [dot] net06 julho 2024 -
![SCP-055 [DESCONOCIDO] (shown) by electromakerproD on DeviantArt](https://images-wixmp-ed30a86b8c4ca887773594c2.wixmp.com/f/83745066-525c-4d43-beb3-de70b41caf74/dczp2bz-76646748-bcd7-4fa6-a911-3e49d5722f3e.png?token=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJzdWIiOiJ1cm46YXBwOjdlMGQxODg5ODIyNjQzNzNhNWYwZDQxNWVhMGQyNmUwIiwiaXNzIjoidXJuOmFwcDo3ZTBkMTg4OTgyMjY0MzczYTVmMGQ0MTVlYTBkMjZlMCIsIm9iaiI6W1t7InBhdGgiOiJcL2ZcLzgzNzQ1MDY2LTUyNWMtNGQ0My1iZWIzLWRlNzBiNDFjYWY3NFwvZGN6cDJiei03NjY0Njc0OC1iY2Q3LTRmYTYtYTkxMS0zZTQ5ZDU3MjJmM2UucG5nIn1dXSwiYXVkIjpbInVybjpzZXJ2aWNlOmZpbGUuZG93bmxvYWQiXX0.FXz27-dKBLymf8ZHwIX4X3Ip5cCkwYlFkN7ho5TEzE8) SCP-055 [DESCONOCIDO] (shown) by electromakerproD on DeviantArt06 julho 2024
SCP-055 [DESCONOCIDO] (shown) by electromakerproD on DeviantArt06 julho 2024 -
 Game Dragon Ball Z Budokai Tenkaichi 3 Hint APK for Android Download06 julho 2024
Game Dragon Ball Z Budokai Tenkaichi 3 Hint APK for Android Download06 julho 2024 -
 Saint Seiya, VS Battles Wiki06 julho 2024
Saint Seiya, VS Battles Wiki06 julho 2024 -
Happy New Year! Thank you for all your support in 2018 – we can't wait to bring even more to Dream League Soccer in 2019!, By Dream League Soccer06 julho 2024
-
/i.s3.glbimg.com/v1/AUTH_08fbf48bc0524877943fe86e43087e7a/internal_photos/bs/2023/U/A/520r4kQoK55oZXtyPMwQ/playstation-vr2-psvr2-5-ps5-funcao-controle-arco-flecha-tensao.jpg) PSVR 2: veja preço, data de lançamento e mais sobre o acessório de PS506 julho 2024
PSVR 2: veja preço, data de lançamento e mais sobre o acessório de PS506 julho 2024 -
 Buster Crabbe The Files of Jerry Blake06 julho 2024
Buster Crabbe The Files of Jerry Blake06 julho 2024